December 15, 2023
Security
October 20, 2023
IoT Security: Safeguarding Your Smart Home and Devices
IoT Security: Safeguarding Your Smart Home and Devices Our homes have become more convenient and efficient than ever before. Smart thermostats, security cameras, voice assistants, and even refr
September 29, 2023
PQC Coalition—Securing the Future of Encryption
By Craig Kennedy PQC Coalition—Securing the Future of Encryption On Tuesday, September 26th, a new coalition of cybersecurity organizations tasked to promote the awareness and adoption of post-quantum cryptography was
July 28, 2023
Frontier Model Forum—Power Players Unite to Make AI Safer
By: Craig Kennedy Frontier Model Forum—Power Players Unite to Make AI Safer On Wednesday July 26th, 2023, Microsoft, OpenAI, Google, and Anthropic jointly announced the launching of the Frontier Model For
June 23, 2023
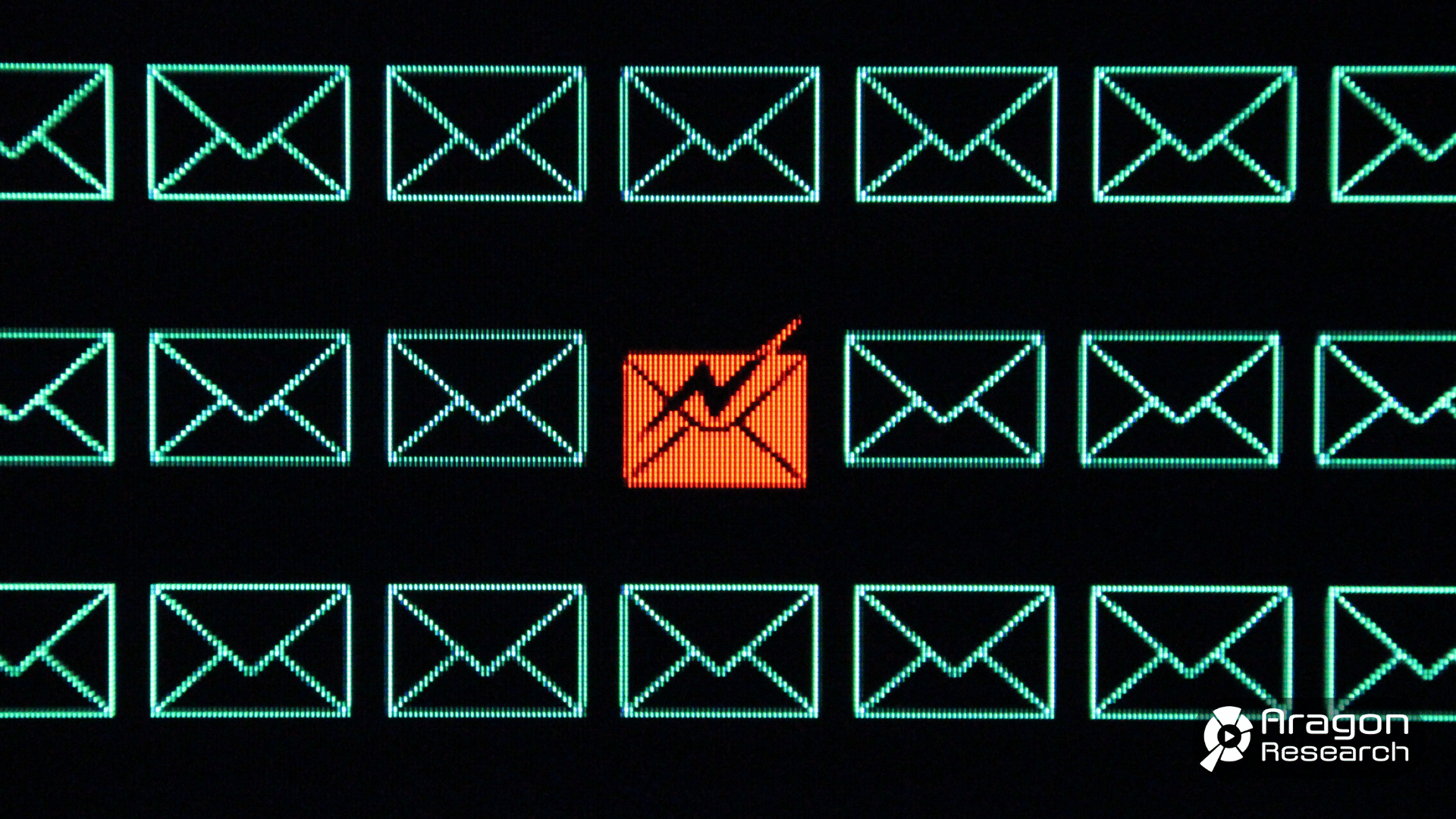
Safeguarding Your Workplace: 5 Types of Email Threats
5 Common Email Threats in the Workplace You Need to Look Out for in 2023 Today, email has become an integral part of our professional lives. However, with the increasing reliance on email communication, the risk of email
May 4, 2023
World Password Day – Is This the Last Anniversary
By: Craig Kennedy World Password Day – Is This the Last Anniversary For the last ten years, the first Thursday in May has been deemed World Password Day. World Password Day was created by Intel in 2013 as a way to re
April 28, 2023
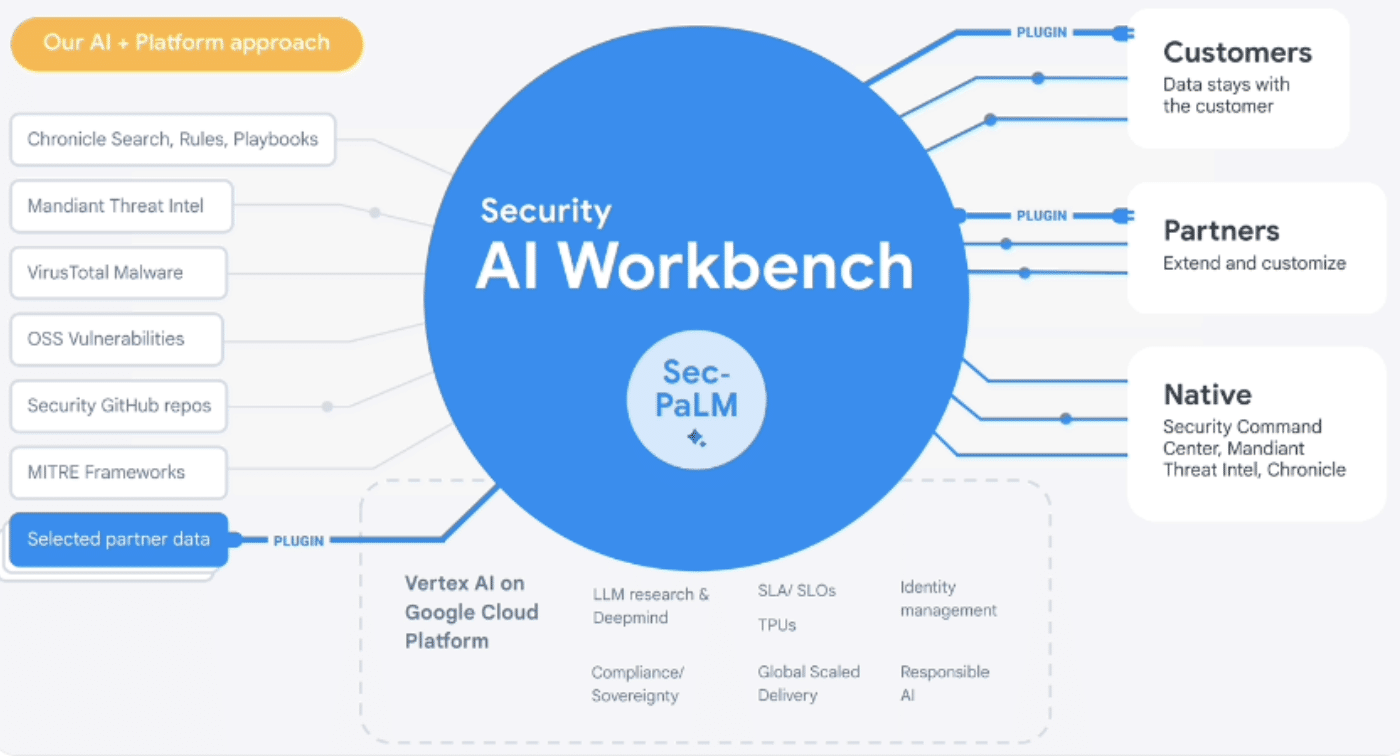
Google Cloud Security AI Workbench – Conversational Security
By Craig Kennedy Google Cloud Security AI Workbench—Conversational Security On Monday April 24TH at the RSA Conference 2023 held in San Francisco, Google Cloud announced it was entering the Generative AI Securi
April 14, 2023
3 Frequently Asked Questions About Security Trends in 2023
By Paula Quiroz Aragon Research's Senior Director of Research, Craig Kennedy, hosted a webinar titled “Trends in Enterprise Security – Act Now to Protect Your Enterprise.” During this webinar, Aragon's seni
April 5, 2023
Operation Cookie Monster Takes a Huge Bite Out of The Dark Web
By: Craig Kennedy Operation Cookie Monster Takes a Huge Bite Out of The Dark Web Genesis Marketplace Taken Down On Tuesday this week, the FBI in collaboration with dozens of law enforcement agencies around the glo
March 29, 2023
Microsoft Security Copilot—Defending the Enterprise at the Speed of AI
By: Craig Kennedy Microsoft Security Copilot—Defending the Enterprise at the Speed of AI On Tuesday March 28th, Microsoft announced its latest use case for ChatGPT technology, Microsoft Security Copilot. Powered
February 24, 2023
The Cost of Supply Chain Security—$250M in Sales
The Cost of Supply Chain Security—$250M in Sales By: Craig Kennedy On February 16th, Applied Materials announced its first quarter 2023 earnings, and in the Q2 Business Outlook section reported a “negative esti
February 10, 2023
What is Data Management?
Today, there is more data than ever before. Professionals and organizations are up against the challenge of organizing a massive amount of data, reading it, and figuring out how to use the data to take b
October 20, 2022
Preventing Account Cloning – Best Practices
Can Account Cloning Be Prevented? By Ken Dulaney In this blog, Vice President of Research at Aragon Research, Ken Dulaney discusses how difficult account cloning may be to prevent. We share the best practices
September 21, 2022
Digital Operations: Keeping Your Infrastructure Secure
By Craig Kennedy Digital Operations: Securing Your Infrastructure In this second edition of the Digital Operations weekly blog series, we’ll be focusing on cyber security as our topic for the week.
August 2, 2012
Cloud: Is Your Cloud Vendor Ready for You?
By Jim Lundy You can't read a technology blog today without getting hit with cloud. The question that is asked most often is, "Are you ready for the cloud?" I'd like to suggest that you flip it and see if your vendor
June 7, 2012
LinkedIn Security Breach: Need to Secure Social Networks and Content
LinkedIn Security Breach Reinforces Need to Secure Social Networks and Content To view a PDF of this First Cut, click here. Author: Jim Lundy, Mike Anderson Topics: Workplace, Social Software Issues: What t
January 6, 2012