Pipelines Become Strategic: The Rise of Ransomware as a Service
by Craig Kennedy and Jim Lundy
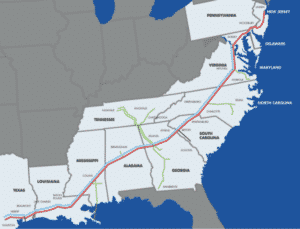
Last weekend Colonial Pipeline, the largest fuel pipeline in the US, carrying 2.5 million barrels a day to Southern and Eastern states, was hacked and shut down. This pipeline alone carries 45% of the diesel, gas, heating oil, and Jet fuel for the East Coast of the United States. This blog talks about the hack and the group that was responsible for it, DarkSide.
The Attack on Colonial Pipeline
Colonial Pipeline was informed on Friday by a ransomware group that its network had been infiltrated and around 100 GB of its data encrypted and taken hostage. The hackers demanded a ransom be paid or their data would be leaked over the internet. Colonial proactively shut down its systems, engaged an outside security firm, and notified local and federal authorities. The shutting down of all its systems had the consequence of halting operations on the entire 5,500 miles of their pipeline, spanning states from Texas to New York.
Analysis
The attack on Colonial Pipeline is just one example of the rising ransomware attacks being perpetrated on enterprises and the public sector. We have talked at length about our infrastructure being vulnerable and this is now a proven example of how bad things can get if organizations fail to take proactive measures to secure their enterprise more seriously.
DarkSide and Ransomware as a Service
DarkSide is a hacker group that was profiled initially in 2020 by Wired magazine. It offers ransomware as a service (RaaS) providing its clients/hackers the use of their ransomware tools for a percentage of any ransom extracted from victims. DarkSide actually provides support to hackers that allow it to target companies and demand payments. Combine this with the ability to purchase stolen credentials on the dark web, and hackers no longer have to be technically savvy to pull off a ransomware attack.
[optin-monster-shortcode id=”ixwm7xwc551w8ok69ild”]Ransomware Is Now a National Security Issue
The selection of such a high visibility target and the major disruption it has caused is shining a bright and unwanted spotlight on DarkSide. A rapid response team consisting of the FBI and other US government agencies working in collaboration with private companies was assembled. This team was able to thwart the attackers on Saturday by identifying and taking offline the cloud system the hackers used in the attack according to Reuters.
What Should Enterprises Do?
Enterprises should ensure all their critical systems are backed up in geographically diverse locations and that backup files are locked and protected from any alterations. Additionally, one of the best and easiest ways to protect the enterprise from unauthorized access is to implement multi-factor authentication (MFA) for all logins on all systems in the enterprise (servers, endpoints, network devices, and SaaS applications).
If there is any uncertainty of your enterprise security status, you should immediately schedule a detailed security assessment of your entire infrastructure and operational processes and procedures, prioritizing your critical infrastructure first.
Bottom Line—Protect your Enterprise
This attack as well as the SolarWinds attack from late last year clearly point out that hackers have not just upped their game, they’ve taken it to an entirely new level. Whether it’s the backing of a nation state or the structural organization of malware or ransomware “as a service,” organizations are at increasing risk of being severely impacted unless strong security measures are put in place. Enterprises and public sector organizations regardless of size must get absolutely serious about security.




Have a Comment on this?